
Getty Pictures
Hackers abused an antivirus service for 5 years with the intention to infect finish customers with malware. The assault labored as a result of the service delivered updates over HTTP, a protocol susceptible to assaults that corrupt or tamper with knowledge because it travels over the Web.
The unknown hackers, who could have ties to the North Korean authorities, pulled off this feat by performing a man-in-the-middle (MiitM) assault that changed the real replace with a file that put in a sophisticated backdoor as a substitute, stated researchers from safety agency Avast at present.
eScan, an AV service headquartered in India, has delivered updates over HTTP since at the very least 2019, Avast researchers reported. This protocol introduced a useful alternative for putting in the malware, which is tracked in safety circles underneath the identify GuptiMiner.
“This subtle operation has been performing MitM assaults concentrating on an replace mechanism of the eScan antivirus vendor,” Avast researchers Jan Rubín and Milánek wrote. “We disclosed the safety vulnerability to each eScan and the India CERT and acquired affirmation on 2023-07-31 from eScan that the problem was mounted and efficiently resolved.”
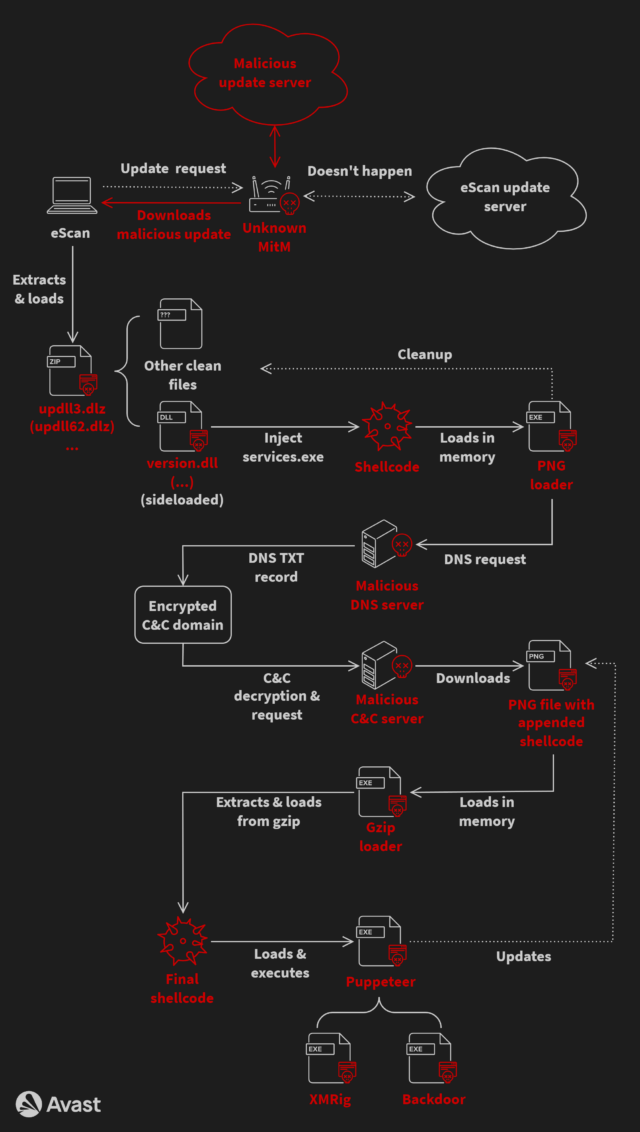
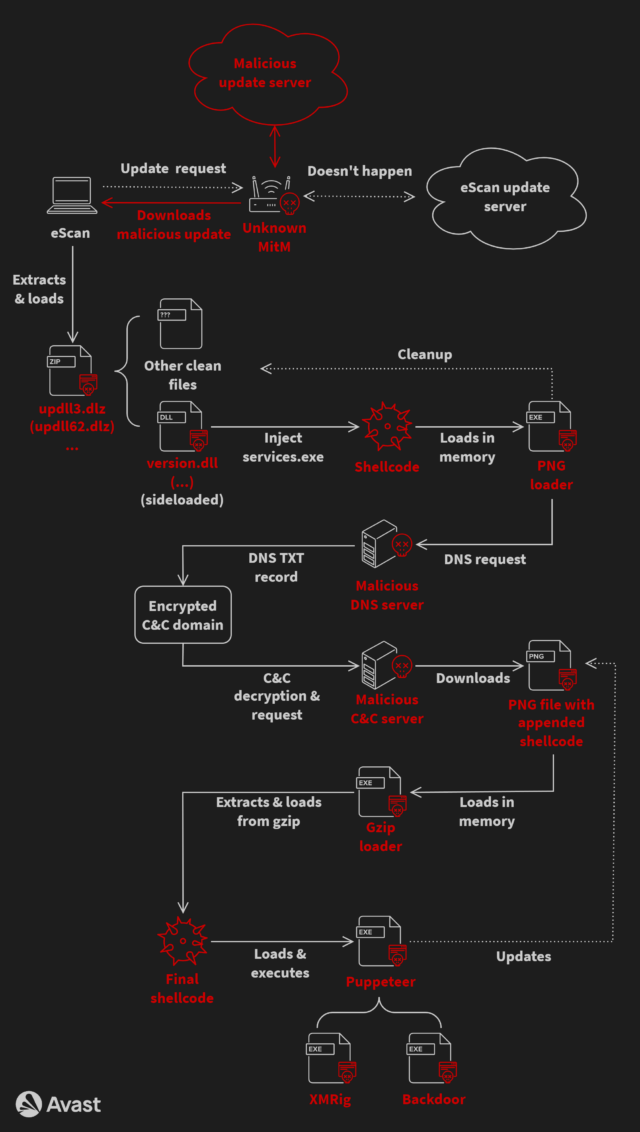
Advanced an infection chain
The complicated an infection chain began when eScan purposes checked in with the eScan replace system. The menace actors then carried out a MitM assault that allowed them to intercept the package deal despatched by the replace server and change it with a corrupted one which contained code to put in GuptiMiner. The Avast researchers nonetheless don’t know exactly how the attackers have been in a position to carry out the interception. They believe focused networks could have already got been compromised one way or the other to route visitors to a malicious middleman.
To decrease the probabilities of detection, the an infection file used DLL hijacking, a method that replaces reputable dynamic hyperlink library information utilized by most Microsoft apps with maliciously crafted ones that use the identical file identify. For added stealth, the an infection chain additionally relied on a customized area identify system (DNS) server that allowed it to make use of reputable domains when connecting to attacker-controlled channels.
Final yr, the attackers deserted the DNS method and changed it with one other obfuscation method often called IP tackle masking. This concerned the next steps:
- Get hold of an IP tackle of a hardcoded server identify registered to the attacker by normal use of the gethostbyname API perform
- For that server, two IP addresses are returned—the primary is an IP tackle which is a masked tackle, and the second denotes an accessible payload model and begins with 23.195. as its first two octets
- If the model is newer than the present one, the masked IP tackle is de-masked, leading to an actual command-and-control (C&C) IP tackle
- The actual C&C IP tackle is used together with a hardcoded fixed string (a part of a URL path) to obtain a file containing malicious shellcode
Some variants of the an infection chain stashed the malicious code inside a picture file to make them tougher to detect. The variants additionally put in a customized root TLS certificates that happy necessities by some focused methods that every one apps should be digitally signed earlier than being put in.
The payload contained a number of backdoors that have been activated when put in on giant networks. Curiously, the replace additionally delivered XMRig, an open-source package deal for mining cryptocurrency.
Avast
GuptiMiner has circulated since at the very least 2018 and has undergone a number of revisions. One searched compromised networks for methods operating Home windows 7 and Home windows Server 2008, presumably to ship exploits that labored on these earlier variations. One other supplied an interface for putting in special-purpose modules that may very well be custom-made for various victims. (This model additionally scanned the native system for saved non-public keys and cryptocurrency wallets.)
The researchers have been shocked that malware that took such pains to fly underneath the radar would additionally set up a cryptocurrency miner, which by nature is often simple to detect. One chance is the attackers’ potential connection to Kimsuky, the monitoring identify for a bunch backed by the North Korean authorities. Through the years, North Korea’s authorities has generated billions of {dollars} in cryptocurrency by means of malware put in on the gadgets of unwitting victims. The researchers made the potential connection after discovering similarities between a recognized Kimsuky keylogger and code fragments used throughout the GuptiMiner operation.
The GuptiMiner assault is notable for exposing main shortcomings in eScan that went unnoticed for at the very least 5 years. In addition to not delivering updates over HTTPS, a medium not inclined to MitM assaults, eScan additionally didn’t implement digital signing to make sure updates hadn’t been tampered with earlier than being put in. Representatives of eScan didn’t reply to an e-mail asking why engineers designed the replace course of this manner.
Individuals who use or have used eScan ought to examine the Avast put up for particulars on whether or not their methods are contaminated. It’s possible that almost all respected AV scanners can even detect this an infection.

Getty Pictures
Hackers abused an antivirus service for 5 years with the intention to infect finish customers with malware. The assault labored as a result of the service delivered updates over HTTP, a protocol susceptible to assaults that corrupt or tamper with knowledge because it travels over the Web.
The unknown hackers, who could have ties to the North Korean authorities, pulled off this feat by performing a man-in-the-middle (MiitM) assault that changed the real replace with a file that put in a sophisticated backdoor as a substitute, stated researchers from safety agency Avast at present.
eScan, an AV service headquartered in India, has delivered updates over HTTP since at the very least 2019, Avast researchers reported. This protocol introduced a useful alternative for putting in the malware, which is tracked in safety circles underneath the identify GuptiMiner.
“This subtle operation has been performing MitM assaults concentrating on an replace mechanism of the eScan antivirus vendor,” Avast researchers Jan Rubín and Milánek wrote. “We disclosed the safety vulnerability to each eScan and the India CERT and acquired affirmation on 2023-07-31 from eScan that the problem was mounted and efficiently resolved.”
Advanced an infection chain
The complicated an infection chain began when eScan purposes checked in with the eScan replace system. The menace actors then carried out a MitM assault that allowed them to intercept the package deal despatched by the replace server and change it with a corrupted one which contained code to put in GuptiMiner. The Avast researchers nonetheless don’t know exactly how the attackers have been in a position to carry out the interception. They believe focused networks could have already got been compromised one way or the other to route visitors to a malicious middleman.
To decrease the probabilities of detection, the an infection file used DLL hijacking, a method that replaces reputable dynamic hyperlink library information utilized by most Microsoft apps with maliciously crafted ones that use the identical file identify. For added stealth, the an infection chain additionally relied on a customized area identify system (DNS) server that allowed it to make use of reputable domains when connecting to attacker-controlled channels.
Final yr, the attackers deserted the DNS method and changed it with one other obfuscation method often called IP tackle masking. This concerned the next steps:
- Get hold of an IP tackle of a hardcoded server identify registered to the attacker by normal use of the gethostbyname API perform
- For that server, two IP addresses are returned—the primary is an IP tackle which is a masked tackle, and the second denotes an accessible payload model and begins with 23.195. as its first two octets
- If the model is newer than the present one, the masked IP tackle is de-masked, leading to an actual command-and-control (C&C) IP tackle
- The actual C&C IP tackle is used together with a hardcoded fixed string (a part of a URL path) to obtain a file containing malicious shellcode
Some variants of the an infection chain stashed the malicious code inside a picture file to make them tougher to detect. The variants additionally put in a customized root TLS certificates that happy necessities by some focused methods that every one apps should be digitally signed earlier than being put in.
The payload contained a number of backdoors that have been activated when put in on giant networks. Curiously, the replace additionally delivered XMRig, an open-source package deal for mining cryptocurrency.
Avast
GuptiMiner has circulated since at the very least 2018 and has undergone a number of revisions. One searched compromised networks for methods operating Home windows 7 and Home windows Server 2008, presumably to ship exploits that labored on these earlier variations. One other supplied an interface for putting in special-purpose modules that may very well be custom-made for various victims. (This model additionally scanned the native system for saved non-public keys and cryptocurrency wallets.)
The researchers have been shocked that malware that took such pains to fly underneath the radar would additionally set up a cryptocurrency miner, which by nature is often simple to detect. One chance is the attackers’ potential connection to Kimsuky, the monitoring identify for a bunch backed by the North Korean authorities. Through the years, North Korea’s authorities has generated billions of {dollars} in cryptocurrency by means of malware put in on the gadgets of unwitting victims. The researchers made the potential connection after discovering similarities between a recognized Kimsuky keylogger and code fragments used throughout the GuptiMiner operation.
The GuptiMiner assault is notable for exposing main shortcomings in eScan that went unnoticed for at the very least 5 years. In addition to not delivering updates over HTTPS, a medium not inclined to MitM assaults, eScan additionally didn’t implement digital signing to make sure updates hadn’t been tampered with earlier than being put in. Representatives of eScan didn’t reply to an e-mail asking why engineers designed the replace course of this manner.
Individuals who use or have used eScan ought to examine the Avast put up for particulars on whether or not their methods are contaminated. It’s possible that almost all respected AV scanners can even detect this an infection.






