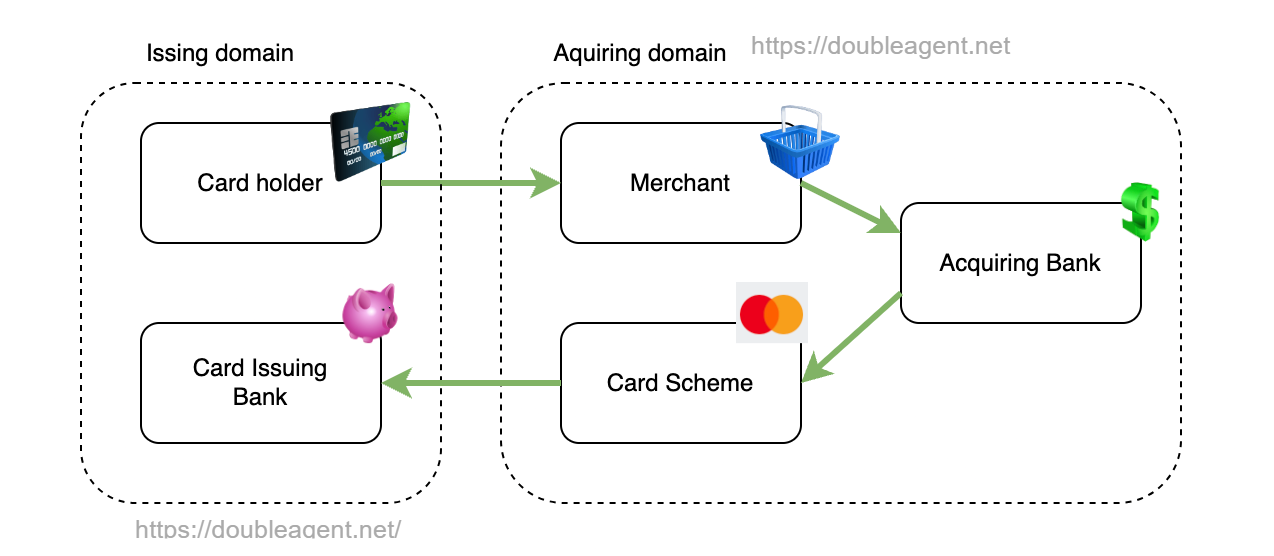
The malware resides within the userspace portion of the interbank swap connecting the issuing area and the buying area. When a compromised card is used to make a fraudulent translation, FASTCash tampers with the messages the swap receives from issuers earlier than relaying it again to the service provider financial institution. In consequence, issuer messages denying the transaction are modified to approvals.
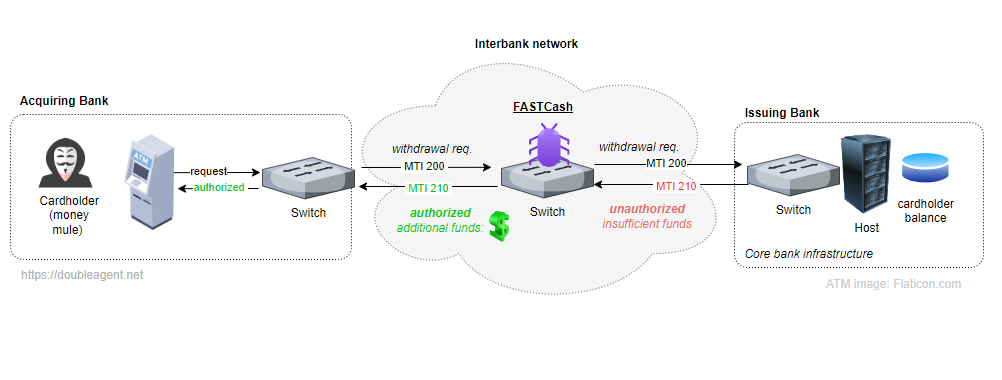
The next diagram illustrates how FASTCash works:
The switches chosen for concentrating on run misconfigured implementations of ISO 8583, a messaging customary for monetary transactions. The misconfigurations stop message authentication mechanisms, similar to these utilized by discipline 64 as outlined within the specification, from working. In consequence, the tampered messages created by FASTCash aren’t detected as fraudulent.
“FASTCash malware targets techniques that ISO8583 messages at a particular intermediate host the place safety mechanisms that make sure the integrity of the messages are lacking, and therefore could be tampered,” haxrob wrote. “If the messages have been integrity protected, a discipline similar to DE64 would possible embrace a MAC (message authentication code). As the usual doesn’t outline the algorithm, the MAC algorithm is implementation particular.”
The researcher went on to clarify:
FASTCash malware modifies transaction messages in a degree within the community the place tampering won’t trigger upstream or downstream techniques to reject the message. A possible place of interception could be the place the ATM/PoS messages are transformed from one format to a different (For instance, the interface between a proprietary protocol and another type of an ISO8583 message) or when another modification to the message is finished by a course of operating within the swap.
CISA stated that BeagleBoyz—one of many names the North Korean hackers are tracked below—is a subset of HiddenCobra, an umbrella group backed by the federal government of that nation. Since 2015, BeagleBoyz has tried to steal practically $2 billion. The malicious group, CISA stated, has additionally “manipulated and, at occasions, rendered inoperable, vital laptop techniques at banks and different monetary establishments.”
The haxrob report gives cryptographic hashes for monitoring the 2 samples of the newly found Linux model and hashes for a number of newly found samples of FASTCash for Home windows.
The malware resides within the userspace portion of the interbank swap connecting the issuing area and the buying area. When a compromised card is used to make a fraudulent translation, FASTCash tampers with the messages the swap receives from issuers earlier than relaying it again to the service provider financial institution. In consequence, issuer messages denying the transaction are modified to approvals.
The next diagram illustrates how FASTCash works:
The switches chosen for concentrating on run misconfigured implementations of ISO 8583, a messaging customary for monetary transactions. The misconfigurations stop message authentication mechanisms, similar to these utilized by discipline 64 as outlined within the specification, from working. In consequence, the tampered messages created by FASTCash aren’t detected as fraudulent.
“FASTCash malware targets techniques that ISO8583 messages at a particular intermediate host the place safety mechanisms that make sure the integrity of the messages are lacking, and therefore could be tampered,” haxrob wrote. “If the messages have been integrity protected, a discipline similar to DE64 would possible embrace a MAC (message authentication code). As the usual doesn’t outline the algorithm, the MAC algorithm is implementation particular.”
The researcher went on to clarify:
FASTCash malware modifies transaction messages in a degree within the community the place tampering won’t trigger upstream or downstream techniques to reject the message. A possible place of interception could be the place the ATM/PoS messages are transformed from one format to a different (For instance, the interface between a proprietary protocol and another type of an ISO8583 message) or when another modification to the message is finished by a course of operating within the swap.
CISA stated that BeagleBoyz—one of many names the North Korean hackers are tracked below—is a subset of HiddenCobra, an umbrella group backed by the federal government of that nation. Since 2015, BeagleBoyz has tried to steal practically $2 billion. The malicious group, CISA stated, has additionally “manipulated and, at occasions, rendered inoperable, vital laptop techniques at banks and different monetary establishments.”
The haxrob report gives cryptographic hashes for monitoring the 2 samples of the newly found Linux model and hashes for a number of newly found samples of FASTCash for Home windows.